See on Scoop.it – Green Energy Technologies & Development
As the reliance on the data center infrastructure continues to grow, organizations will need to use model-based analytics to help make better IT decisions.
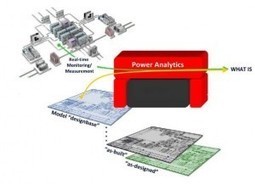
Download this white paper to see how the use of model-based metrics is directly analogous to business analytics. With the complexity of today’s modern systems – without these metrics – management and financial decisions would be nearly impossible. As the reliance on the data center infrastructure continues to grow, organizations will need to use model-based analytics to help make better IT decisions. By utilizing model-based management, organizations will be able to see the powerful link to the overall value chain of designing, building and operating a data center.
See on www.datacenterknowledge.com